Software Deployment Lifecycle: The route from development to production is crucial to customer value as organizations adopt cloud native and everything as code. The “pathway to deploy,” or process, involves many complex stages and decisions that might affect an organization’s capacity to provide software rapidly, consistently, and at scale.
The first post in this series explores the complexities and options for a seamless and effective deployment pathway.
Enterprise cloud-native software development is constantly changing, thus this post gives a maturity model and building blocks to speed the software supply chain lifecycle.
Deployment Pathway to roadmap
Several parties and moving elements must collaborate to hasten deployment. IBM offer a 4-stage implementation, as explained below.
Stage 1: Development Automation
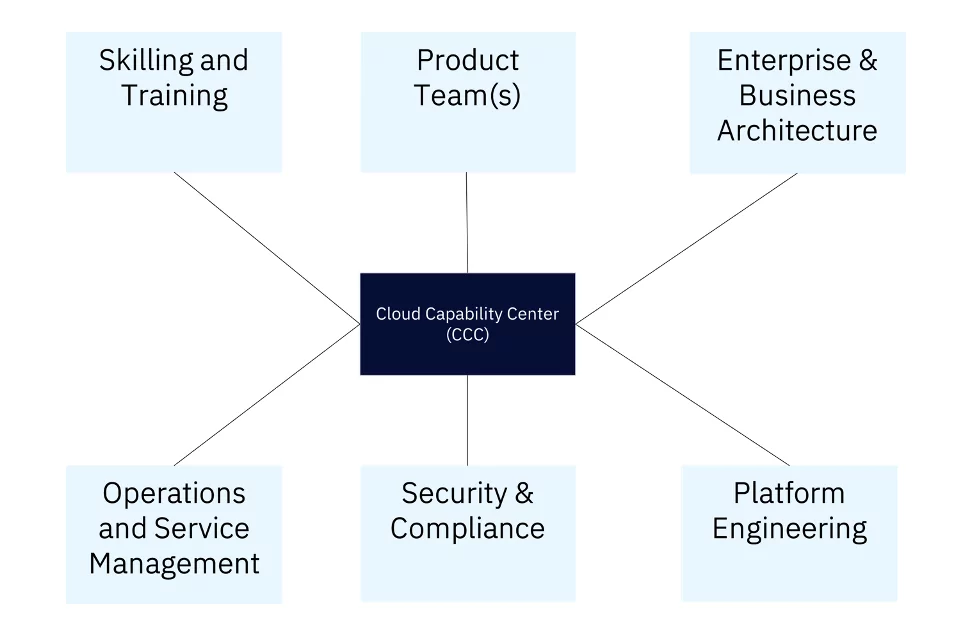
Automation is a good place to start because infrastructure and pipeline automation are self-contained inside the development team. Building an enterprise database of CI/CD/CT and Ops patterns with tooling integrations to automate core development and testing is the focus at this level. Automation of testing capabilities (test data preparation and execution of test cases across different systems is mainly semi-automated) is the hardest element of this stage due to enterprise complexity. Overall, the Cloud Capability Centre (CCC) or core team drives transformation alongside application and platform teams.
Stage 2: Establish pattern-driven model
CCC (or its equivalent) works with the architectural board to create repeatable patterns, including atomic and composite application patterns for cloud services. Architecture review and other review processes are updated to institutionalize pattern-centric architecture representations, with a backlog for platform engineering and CCC to develop these patterns as code. Aids adoption and acceleration. Eventually, the applications become patterns that standardize development models. Using patterns like highly available multi-region architectures, business continuity, resiliency, and security teams will recognize and accelerate approval gates in a standardized manner. This alignment depends on partner organizations co-creating these patterns.
Stage 3: Self-service, cross-functional integration
Many organizations in enterprises desire cloud applications to match their guidelines and best practices. Integration of cross-functional teams like security, compliance, and FinOps is done through automation, tooling, defined patterns, or self-service. This emphasizes meaningful team participation from earlier stages. Important elements of this stage:
- Build and align high-availability patterns with resiliency teams to accelerate reviews and show compliance.
- Codify security and compliance requirements into patterns and enforce them on the platform as policies.
- Integrate vulnerability scans, policy check tools (like cloud formation guard for AWS), and container security with shift-left pipelines to validate addresses.
- Enterprise records teams can investigate data classification and retention patterns, while FinOps teams can check tagging and quota adherence.
- Create AuthN/AuthZ integration patterns to abstract nuances and standardize application, data, and service authentication and authorization.
- Generate resource files from IaC execution and import them to firewall systems to automate firewall.
- Platform Engineering corporate catalog with self-service features.
Stage 4: Automated software deployment
This level decentralizes and decouples enterprise groups while automating and integrating them with DevSecOps. One example is change management automation, including release note creation, where the system automatically creates full change review checklists using data from various interconnected systems. This boosts review credibility, efficiency, and accuracy. This holistic strategy boosts company operating efficiency and risk avoidance.
Path to deployment: Cloud-native model components
Let’s examine several acceleration software deployment use scenarios.
Example 1: Persona-centric IaC codification
Persona- and pattern-based IaC codification speeds development and evaluation.
Product teams must manually code and stakeholders must manually review each issue, which takes time. Product teams can build stakeholder trust and review efficiency by coding these in hardened discrete or composite patterns with Bootstrap code and acceleration.
Example 2: Shift-left security and policy validation
Automation of infrastructure security, compliance, and other policies in CI/CD pipeline. This guarantees that installed infrastructure meets enterprise policies before software deployment. This can be done with cloud provider and open-source tools like Checkov, Cloud formation guard, and cfn-nag. Security teams write policy validation rules, and product teams integrate them into CI/CD/CT pipelines before cloud infrastructure is provisioned.
Example 3: Automated review compliance evidence gathering
Cross-functional cloud platform, security, and compliance teams automate evidence collection to speed up evaluations. This usually requires querying deployed cloud resources using Cloud APIs and creating compliance evidence and posture. Product teams could conduct self-service or DevOps pipeline automation to determine compliance posture and automatically capture review data. When evidence is captured automatically and reviewed hands-free, maturity grows.
Example 4, integrated patterns and pipeline toolkit
Creating composite cloud-native patterns like AWS Active-Active Serverless APIs requires numerous separate patterns. Patterns include:
- Cloud services: Route53, API Gateway, Lambda, Dynamo DB, IAM, CodeDeploy, CodeBuild, CodePipeline, CodeCommit.
- Nonfunctional requirements include AuthN/AuthZ, multi-region active-active software deployment, security at rest and in transit, tracing, logging, monitoring, dashboards, alerting, failover automation, and health checks.
- Integration of enterprise tools including Code Quality, SAST, DAST, Alerting, Test Management, tracking, and planning.
A one-click solution would let product teams choose the proper pattern to produce Bootstrap code that merges many codified patterns from previous use cases.
Methods of Software deployment
According to the image below, the CCC (or similar) must collaborate with multiple organization groups to establish a delivery model.
The delivery model deployment path includes these steps:
- Define the full application lifecycle phase, activity, deliverable, and dependent group path to software deployment.
- Create various squads to focus on different software deployment aspects.
- Plan a squad flex strategy to bring in support groups as needed.
- Create Cloud Capability Center squad backlogs and start capability development.
- Follow the 4-stage maturity paradigm to track enterprise maturity.
- Product teams and stakeholders should be formed during backlog refinement and prioritization.
- Stay focused on automation adoption. Automation and adoption are key to pathway to deploy success.
- Manage deployment pathway knowledge and planning centrally.
- Help product teams include these tasks into their delivery plans with project tracking and agile collaboration platforms like Jira.
- Measure pathway to implement phase gate SLAs and track SLA improvement as capabilities advance.
Consider why cloud transition may not provide full value and identify release lifecycle acceleration as a critical barrier to limit the deployment channel. Pathway to deploy can help different groups expedite the full software supply chain lifecycle beyond development and testing. The 4-stage roadmap begins with DevSecOps and patterns adoption and progresses to product engineering culture. Product teams should decentralize their collaboration with corporate units to use automation and self-service. The maturity model encourages firms to start small and scale progressively, and our delivery approach makes this complex path predictable.

[…] software applications with antiquated systems are often hard to modify, notoriously more expensive to repair, […]