As of right now, both incoming and outgoing Resolver endpoints can use the DNS over HTTPS (DoH) protocol with Amazon Route 53 Resolver. As the name implies, DoH allows data sent for Domain Name System (DNS) resolutions to be encrypted via HTTP or HTTP/2 over TLS.
By using TLS encryption to prevent eavesdropping and modification of DNS data during communication between a DoH client and the DoH-based DNS resolver, DoH improves security and privacy.
This aids in the implementation of a zero-trust architecture, in which all network traffic is encrypted and no actor, system, network, or service operating inside or outside of your security perimeter is trusted. Utilizing DoH also facilitates adherence to suggestions like those outlined in this US Office of Management and Budget (OMB) memo.
Support for DNS via HTTPS in Amazon Route 53 Resolver
In hybrid cloud setups, you can utilize Amazon Route 53 Resolver to resolve DNS queries. For instance, it permits DNS requests from any location inside your hybrid network to be accessed by AWS services. You can configure both inbound and outgoing Resolver endpoints to achieve this:
- DNS queries from your on-premises network or another VPC can reach your VPC through inbound resolver endpoints.
- DNS requests can be sent from your VPC to another VPC or your on-premises network using outbound resolver endpoints.
Following the configuration of the Resolver endpoints, you can create rules that indicate which domain names you wish to have forwarded (inbound) and outbound (from your VPC to an on-premises DNS resolver).
You may now choose the protocols to utilize when creating or updating an inbound or outbound Resolver endpoint:
- DNS over port 53 (Do53), which transmits packets via TCP or UDP.
- DNS over HTTPS (DoH), encrypts the data with TLS.
- Both, depending on the DNS client’s preference.
- There is a particular implementation (DoH-FIPS) for incoming endpoints in order to ensure FIPS compliance.
Let’s examine how this functions in real life
Using the Amazon Route 53 Resolver with DNS over HTTPS
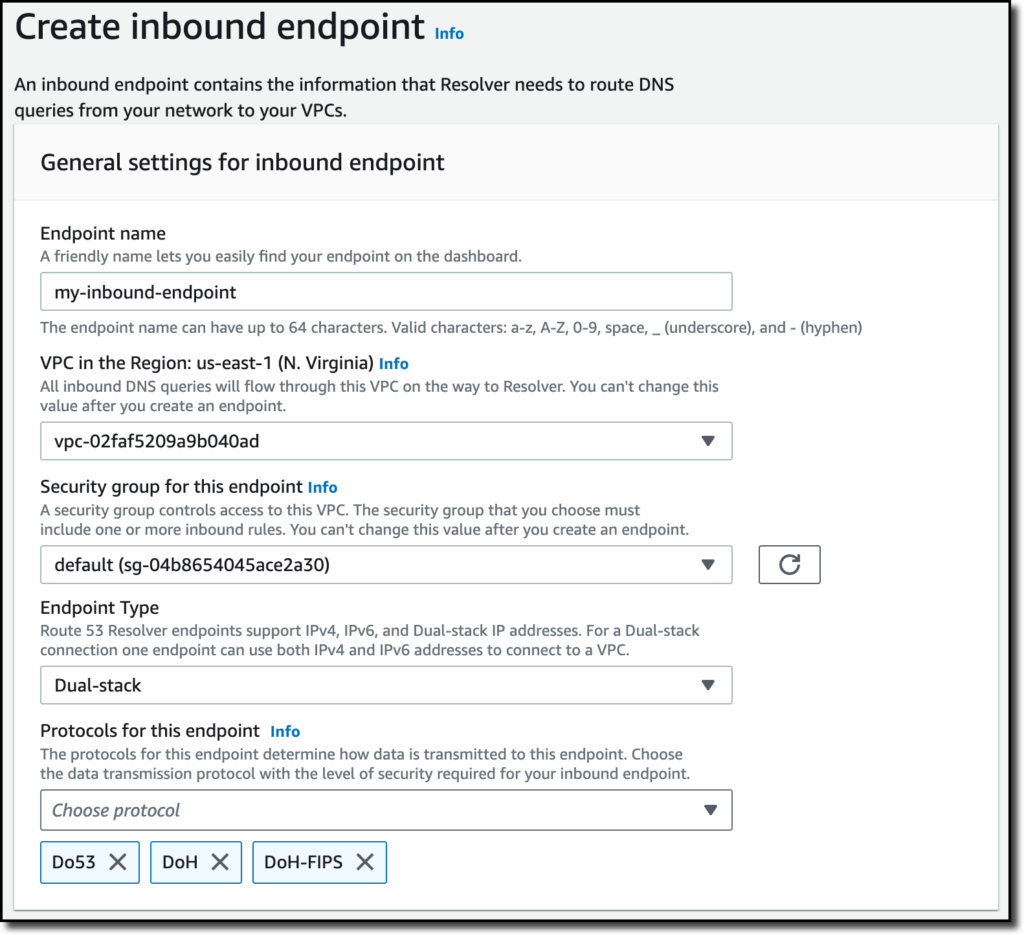
You can select Inbound endpoints in the Route 53 console by going to the Resolver part of the navigation pane. You can select Create inbound endpoint there.
You can choose the security group, the VPC, the endpoint type (IPv4, IPv6, or dual-stack), and then enter the endpoint’s name. In the Protocols for this endpoint option, you can choose Do53, DoH, and DoH-FIPS to permit the use of both encrypted and unencrypted DNS resolutions.
Then set up the IP addresses for DNS queries after that. You can choose two Availability Zones and a subnet for each. You may use the option to have the IP addresses automatically chosen for this setup from the subnet’s available addresses.
Once the incoming endpoint has been created, You can set up my network’s DNS server to route requests for the amazonaws.com domain, which is used by AWS service endpoints, to the IP addresses of the inbound endpoints.
In a similar manner, you may establish an outgoing Resolver endpoint and choose Do53 as well as DoH as the protocols. Next, you design forwarding rules that specify which domains the outgoing Resolver endpoint in my network should forward queries to for DNS servers.
DNS resolutions are now secured when DNS clients in my hybrid environment utilize DNS over HTTPS in their requests. In the setting of inbound and outgoing endpoints, you have the option to impose encryption and choose only DoH.
Important information
All AWS Regions where Route 53 Resolver is available, including GovCloud Regions and Regions based in China, now support DNS over HTTPS for Amazon Route 53 Resolver.
The default DNS protocol for incoming and outgoing Resolver destinations is still port 53. Thus, unless you intend to switch from HTTPS to DNS, you don’t need to upgrade your current automated tools.
Using DNS over HTTPS with Resolver endpoints is free of charge. See Route 53 price for further details.
With Amazon Route 53 Resolver, start using DNS over HTTPS to improve security and privacy for your hybrid cloud settings.

[…] attacks, which primarily use quick UDP internet connections (QUIC) for reflection and domain name system (DNS) and simple service discovery protocol (SSDP) in their attacks. Interestingly, QUIC is becoming a […]