Amazon EBS Snapshot Lock: To improve adherence to your data preservation standards, you can now lock certain Amazon Elastic Block Store (Amazon EBS) snapshots. You have the ability to protect important backups against inadvertent or intentional deletion, including ransomware attacks, by locking snapshots, which cannot be removed until the lock is released or expires.
Why Locking Is Necessary
EBS snapshots are used by AWS customers for data migration, disaster recovery, backups, and compliance. In addition to making sure that the snapshots are indeed Write Once Read Many (WORM), customers in the financial services and healthcare industries frequently have to adhere to strict compliance guidelines with set retention periods. Several AWS accounts with one-way “air gaps” between them are used by customers’ deployed solutions to meet these needs.
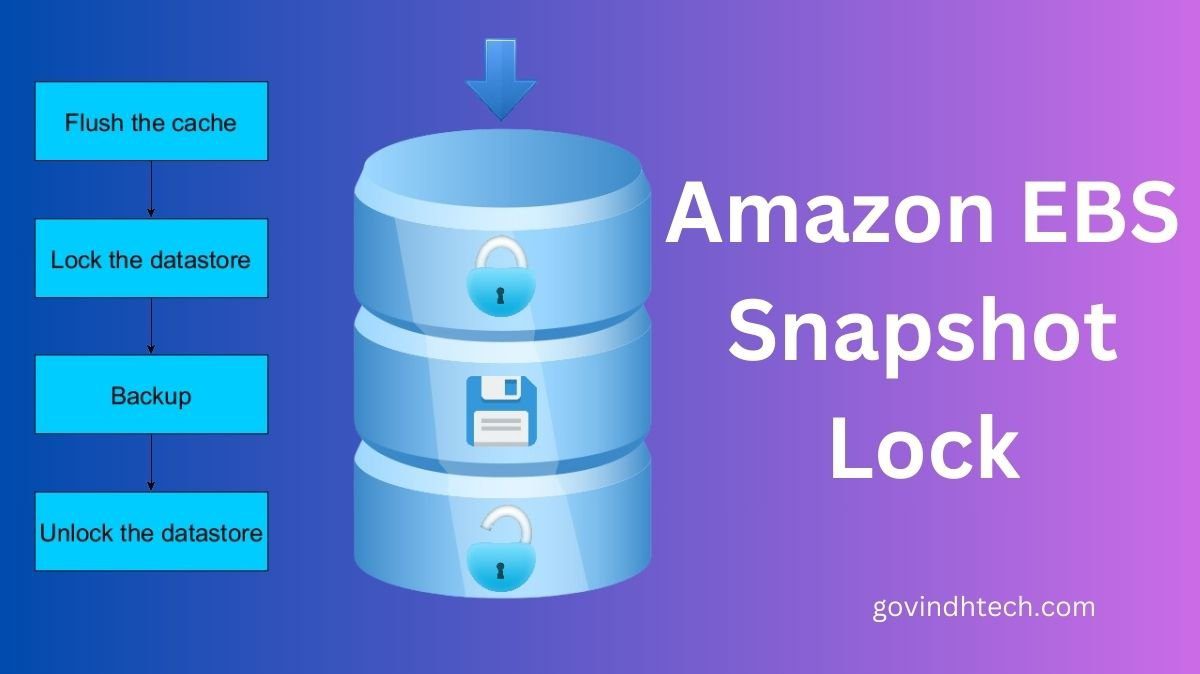
Locking EBS Snapshots
Without requiring proprietary solutions, the new EBS Snapshot Lock feature assists you in meeting your retention and compliance requirements. A lock length of one day to about 100 years can be used to lock both new and old EBS snapshots. The snapshot cannot be erased and is locked for the allotted amount of time.
Best Practices for Snapshot Lock
Governance: With this mode, no user is able to remove a snapshot. On the other hand, the lock can be erased, its length altered, and its mode switched from Governance to Compliance with the appropriate IAM permissions.
Compliance: Using this mode shields snapshots from being accessed by the root user or any other IAM user. Following a 72-hour cooling-off time, the mode cannot be altered and neither the snapshot nor the lock can be removed until the lock length has passed. The lock time can be extended, but not shortened, with the appropriate IAM rights.
You can still share and copy snapshots in any mode. Not only may they be archived to the inexpensive Amazon EBS Snapshots Archive tier, locks can also be placed on previously archived snapshots.
AWS can create and manage locks on their EBS snapshots programmatically by using new API functions:
LockSnapshot: This feature allows you to change the parameters of an already-locked snapshot or lock it in governance or compliance mode.
Open a snapshot that is in compliance mode or in governance mode while it is still inside the cooling-off period by using the UnlockSnapshot function.
Get details about the lock status of AWS snapshots with the possibility to filter based on the lock’s current condition by using the DescribeLockedSnapshots function.
The ec2:lockSnapshot, ec2:UnlockSnapshot, and ec2:DescribeLockedSnapshots permissions are necessary for IAM users to access these features.
Some Information
Regarding this new functionality, bear the following in mind:
AWS Backup: This tool autonomously controls the retention of the snapshots it generates. It is not advised that you lock them.
Cost: Using this feature does not incur any additional fees. For the storage of snapshots and archived snapshots, you pay the standard fees.
Availability: EBS Snapshot Locking is accessible in every commercial Amazon region.
KMS Key Retention – You must ensure that the key will stay valid for the duration of the snapshot if you are encrypting your EBS volumes and snapshots with customer-managed AWS Key Management Service (AWS KMS) keys.

[…] go to partyrock.aws click Sign in, and use my Google, Apple, or Amazon account to log in to get […]